Introduction
In an increasingly interconnected world, border security has become a critical concern for nations worldwide. To address the challenges posed by international travel, governments have turned to biometric technologies as a means to enhance security measures at the border. Biometrics offers the potential for accurate identity verification, allowing border control authorities to identify individuals quickly and reliably. However, implementing biometrics raises questions about striking the right balance between security, privacy, and convenience.
This blog explores the challenges and considerations involved in finding that delicate foothold.
Enhanced Security
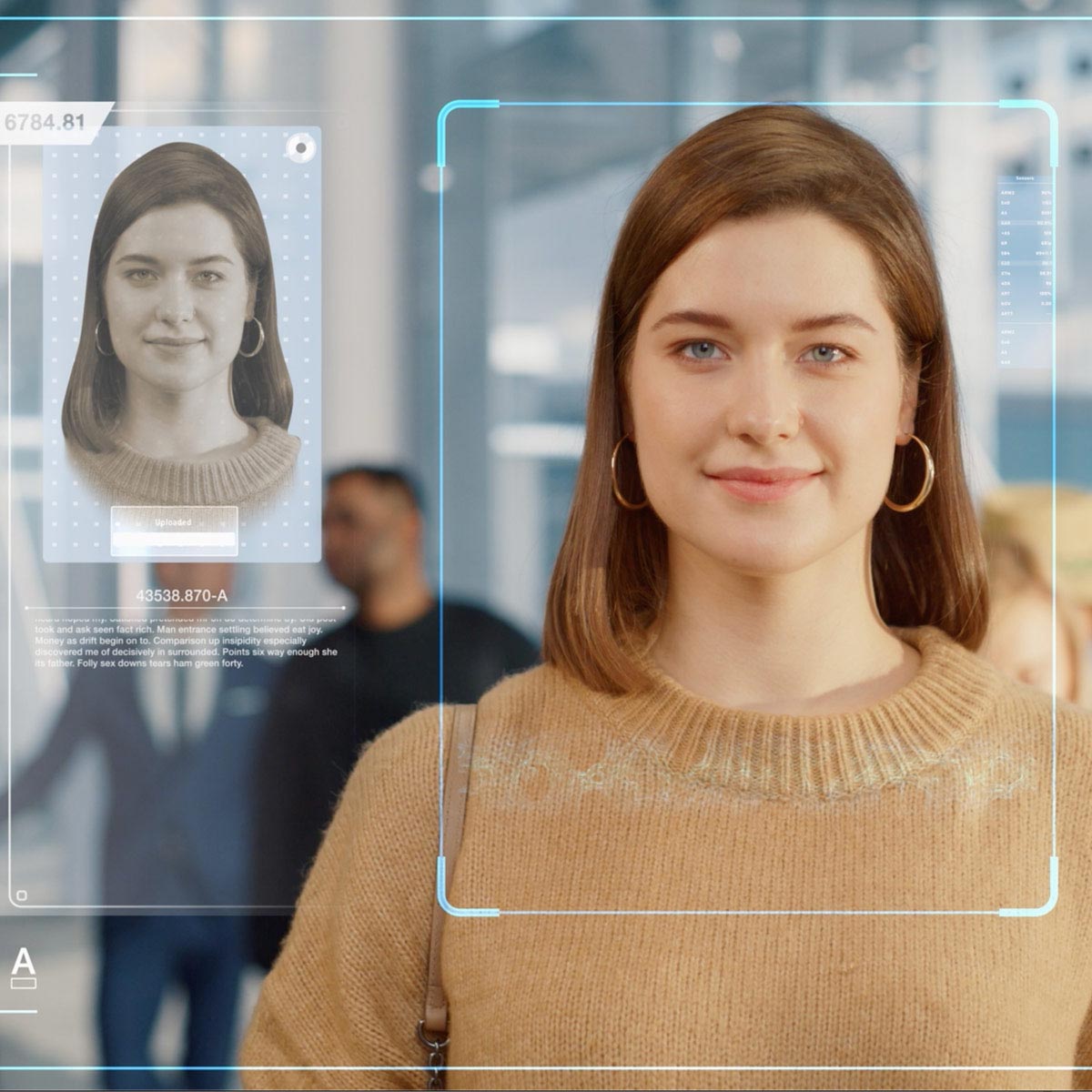
One of the primary drivers behind the adoption of biometrics at the border is the desire to enhance security. Biometric identification methods such as fingerprint, iris, and facial recognition offer a higher level of accuracy than traditional identification methods like passports and ID cards.
In the case of the U.S. Customs and Border Protection (CBP), their Simplified Arrival system is utilizing Biometric Facial Comparison as one of the ways they’re working to secure the borders, while also delivering an enhanced travel experience that’s safer and faster. The use of Biometric Facial Comparison reduces the risk of imposter threats, doesn’t require direct contact with another person, and is more efficient when confirming the identity of the traveler.
Additionally, by employing biometric data, border control authorities can better identify individuals, verify their identities, and detect any red flags associated with criminal activity or security threats. This further contributes to the overall security of a nation’s borders, mitigating potential risks and safeguarding its citizens.
Privacy Concerns
While the use of biometrics provides significant security benefits, it also raises legitimate privacy concerns. Biometric data is highly personal and sensitive since it is unique to each individual. Collecting, storing, and sharing such data must be done with utmost care to protect individuals’ privacy rights.
In the case of CBP, per their website: “Hosted within a secure, cloud-based environment, facial comparison software does not store biographic data for any travelers. CBP retains U.S. citizens photos for no more than 12 hours after identity verification, and only for continuity of operations purposes. CBP enrolls in-scope non-U.S. citizen travelers in the DHS Biometric Identity Management System (IDENT) as a biometric confirmation of arrival.”
They make no qualms about ensuring the privacy of travelers who partake in this process – ensuring they know that this isn’t a surveillance program, and that all cameras and signage are on display for everyone to see. It’s a purposeful maneuver to differentiate itself from surveillance systems, whereby people may not know they’re being recorded.
Transparency, informed consent, and clear data retention policies are essential elements in building trust and addressing privacy concerns. In the end, should participating in Biometric Facial Comparison still not be for you, travelers continue to have the option of requesting a manual verification with a CBP officer.
Maintaining Convenience
Finding the balance between security and convenience is another critical aspect of deploying biometric systems at the border. Travelers value efficient and hassle-free processes, and any disruptions or delays can negatively impact their experience. Biometrics can offer significant convenience by reducing queuing times, automating processes, and expediting identity verification. The ultimate goal is to balance the security and privacy users need with the continued convenience of a process that is entirely user-friendly.
Take, for instance, Aware’s President and CEO, Robert Eckel, who encountered a snafu when trying to log into the SSA’s knowledge-based authentication system. It wasn’t until the SSA transitioned to a biometric-based authentication system that logging into a given account became a breeze.
With that in mind, striking the right balance is crucial to avoid excessive intrusions on personal privacy or creating systems that are overly complex and burdensome for travelers to navigate. User-friendly interfaces, streamlined processes, and clear communication are essential for maintaining convenience without compromising security.
Technical Challenges
Implementing biometric identity management systems at border crossings involves overcoming various technical challenges.
First, ensuring the accuracy and reliability of biometric data matching algorithms is paramount. Any errors in identification can lead to false positives or negatives, potentially causing inconvenience or even discrimination. Rigorous testing, algorithm updates, and continuous monitoring are crucial to minimize these risks.
Second, interoperability between different systems and databases is essential, especially in an international context. Harmonizing standards and protocols enables seamless data sharing and cooperation among nations, enhancing security while facilitating smooth travel experiences for individuals.
Ethical Considerations
Biometric technologies also bring ethical considerations to the forefront. As governments deploy these systems, they must ensure transparency, fairness, and accountability. Clear guidelines should be established to prevent misuse of biometric data, profiling, or discrimination based on race, gender, or any other protected characteristics. Additionally, ongoing oversight and audits are necessary to ensure compliance with ethical standards and to address any potential abuses or vulnerabilities.
Conclusion
Finding the right balance between security, privacy, and convenience with biometrics at the border is a complex challenge. Governments must navigate the technical, legal, and ethical dimensions to implement effective systems that enhance security while respecting privacy rights and maintaining traveler convenience. Achieving this balance requires robust legal frameworks, clear communication, and ongoing collaboration between stakeholders. By striking this delicate foothold, nations can create a border control environment that is both secure and respectful of individuals’ rights, contributing to safer and more efficient international travel.